In 2025, crypto users lost over $18 billion to hacks, exploits, and scams. Most of those losses had one thing in common: someone trusted the wrong intermediary with their funds.
But here’s the thing — you don’t have to trust anyone. Not a company, not a middleman, not even the platform you’re using. Smart contract escrow replaces human trust with mathematical certainty, and understanding how it works is the difference between sleeping soundly and refreshing Etherscan at 3 AM.
In this guide, we’ll break down exactly how smart contract escrow protects your funds — from the code-level security mechanisms to the dispute resolution systems that kick in when things go sideways. Whether you’re evaluating crypto escrow for the first time or comparing platforms, this is your security deep-dive.
Table of Contents
- Why Security Matters in Crypto Escrow
- What Makes Smart Contract Escrow Secure?
- Payment Protection Mechanisms
- Custodial vs Non-Custodial: A Security Comparison
- Dispute Resolution in Smart Contract Escrow
- Common Attack Vectors and How Escrow Contracts Defend Against Them
- How to Verify a Smart Contract Escrow is Safe
- FAQ
Why Security Matters in Crypto Escrow
The entire point of escrow is to protect both parties in a transaction. But if the escrow itself isn’t secure, you’ve just moved the risk — not eliminated it.
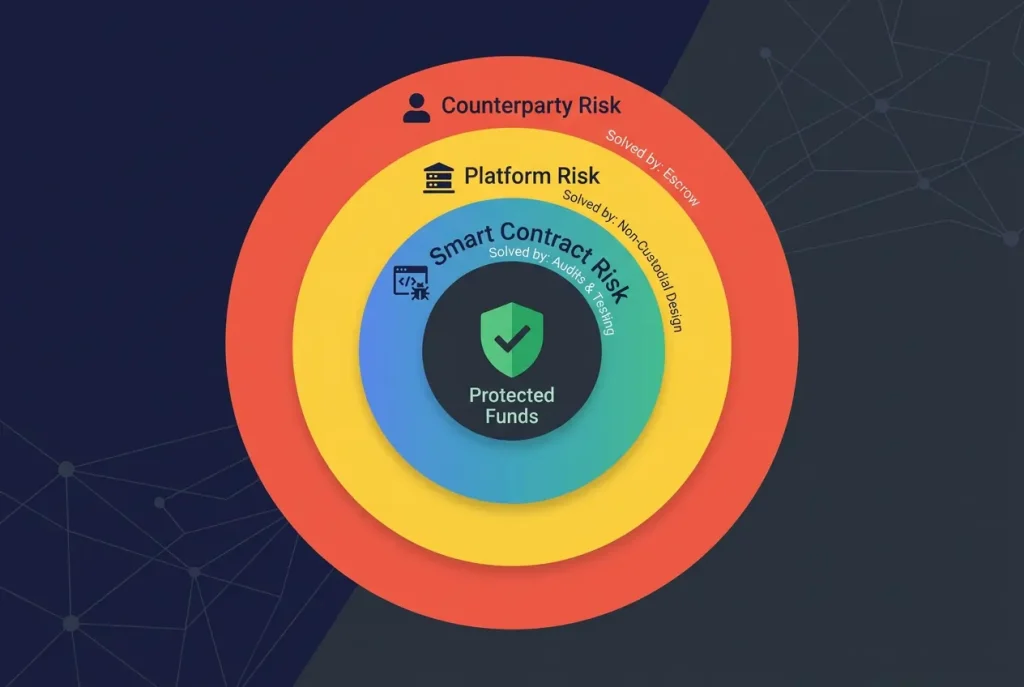
Consider the three ways a crypto transaction can go wrong:
- Counterparty risk — the other person scams you (escrow solves this)
- Platform risk — the escrow provider steals or loses your funds (security solves this)
- Smart contract risk — a bug in the code causes unintended behavior (audits solve this)
A well-designed smart contract escrow eliminates all three. A poorly designed one might solve #1 while introducing #2 and #3. That’s why understanding the security model isn’t optional — it’s the whole game.
What Makes Smart Contract Escrow Secure?
Smart contract escrow on Ethereum isn’t just “code holding money.” It’s a carefully engineered system with multiple security layers working together. Let’s unpack each one.
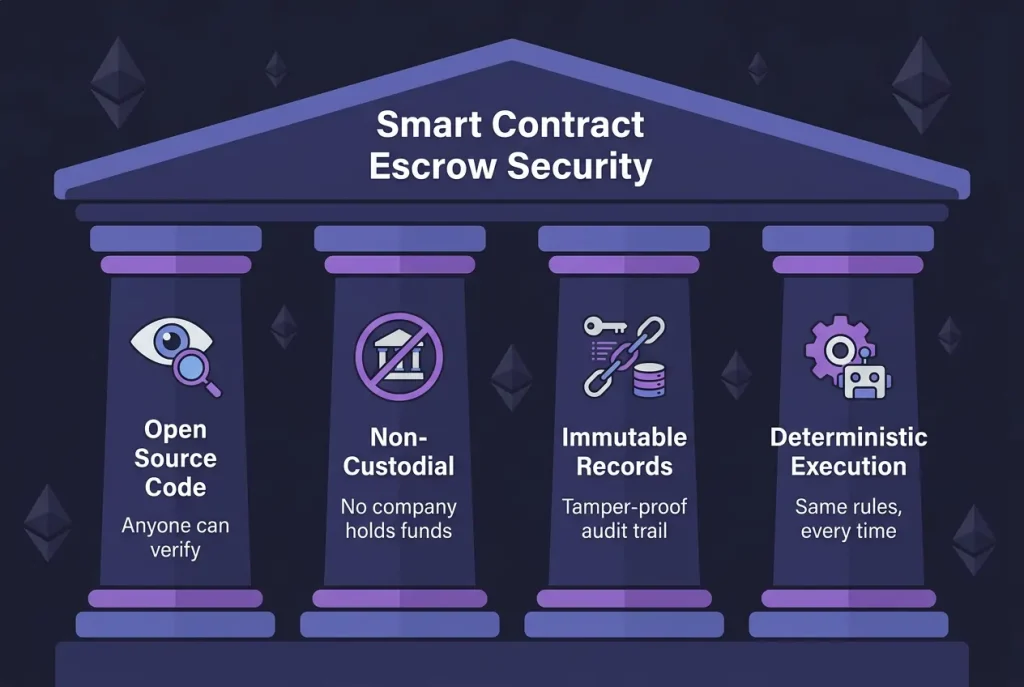
Open Source, Verifiable Code
The first rule of crypto security: don’t trust, verify.
With smart contract escrow, the rules governing your funds aren’t hidden behind a corporate firewall. They’re published on the blockchain for anyone to read, audit, and verify. Every function — how funds are deposited, when they can be released, what triggers a dispute — is visible in the source code.
This is fundamentally different from traditional escrow, where you’re trusting a company’s internal processes that you can never inspect. With a verified Ethereum smart contract, a developer in Tokyo can audit the same code as a security researcher in Berlin. The rules are the same for everyone, always.
Non-Custodial Architecture
Here’s the security feature that matters most: nobody holds your private keys.
In a non-custodial escrow, funds are locked in a smart contract — not in a company’s wallet. The platform that built the escrow can’t access your funds. The developers can’t move them. Even if the company behind the platform disappeared tomorrow, your funds would still be governed by the immutable contract on Ethereum.
This is the critical distinction between custodial and non-custodial escrow, and it’s worth understanding deeply (more on this below).
Immutable Transaction Records
Every action in a smart contract escrow is permanently recorded on the Ethereum blockchain:
- When funds were deposited (and by whom)
- When the seller accepted the terms
- When fulfillment was marked
- When funds were released (and to whom)
- If a dispute was opened and how it was resolved
This creates a complete, tamper-proof audit trail. No one can claim “I never received the funds” when the blockchain says otherwise. No one can alter the record after the fact. It’s the ultimate receipt.
Deterministic Execution
Smart contracts don’t have bad days. They don’t play favorites. They don’t “interpret” the rules differently depending on who’s asking.
When a smart contract says “release funds to the seller when the buyer calls the release function,” that’s exactly what happens. No exceptions, no delays, no “we’ll review your case in 5-7 business days.” The code executes identically every single time, for every single user.
This determinism is what makes smart contract escrow fundamentally more predictable than any human-operated system.
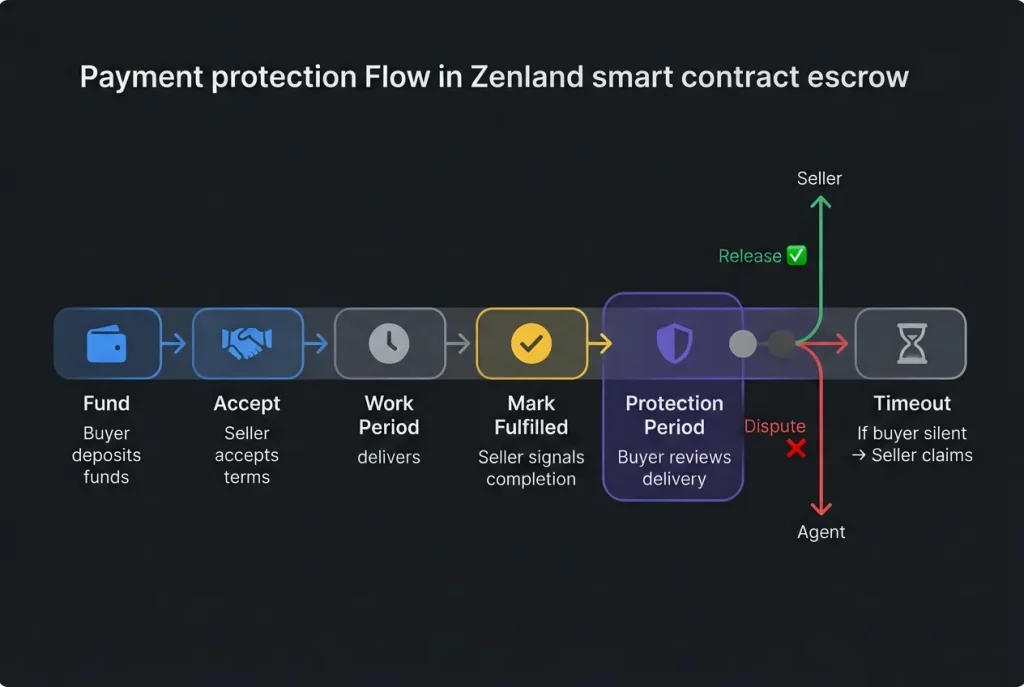
Payment Protection Mechanisms
Security isn’t just about preventing hacks — it’s about protecting both parties throughout the entire transaction lifecycle. Here’s how smart contract escrow builds protection into every stage.
Locked Funds: No Unilateral Withdrawals
Once funds enter the escrow contract, neither party can withdraw them alone. The buyer can’t pull their money back after the seller starts working. The seller can’t grab the funds before delivering. The smart contract enforces a strict state machine — funds only move when the right conditions are met by the right party.
This is the core payment protection mechanism, and it’s what makes the “who sends first?” problem disappear entirely.
Time-Based Protections
Smart contracts can enforce deadlines that protect both sides:
Buyer protection period: After the seller marks delivery as complete, the buyer gets a defined window to review. During this time, only the buyer can release funds or open a dispute. The seller can’t rush the process.
Auto-release on timeout: If the buyer receives delivery but goes silent — never releasing, never disputing — the protection period eventually expires. At that point, the seller can claim their payment. This prevents buyers from holding funds hostage indefinitely.
Agent response windows: If a dispute is opened and an agent is invited, they have a defined timeframe (typically 7 days) to respond. If they don’t, the dispute process resets, preventing indefinite limbo.
The Seller’s Escape Hatch: Voluntary Refund
Here’s a protection mechanism that’s often overlooked: the seller can always initiate a refund.
If a seller realizes they can’t deliver, or if circumstances change, they can refund the buyer at any point. This prevents the nightmare scenario of funds being permanently locked because a seller disappeared mid-project. It’s a safety valve that keeps the system flexible without compromising security.
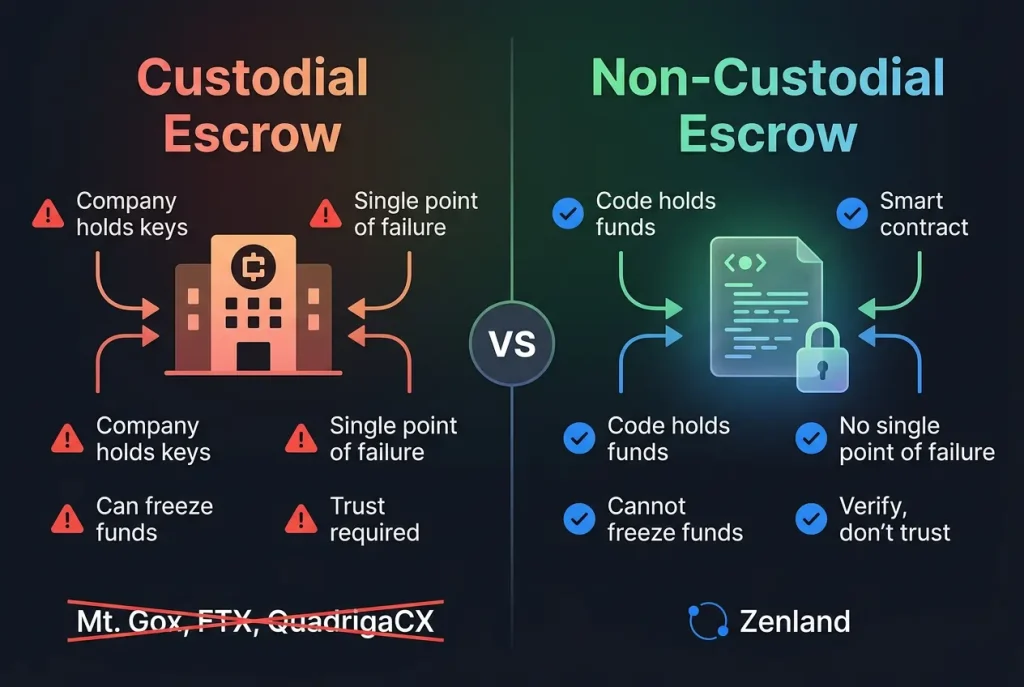
Custodial vs Non-Custodial: A Security Comparison
This is the most important security decision you’ll make when choosing a crypto escrow platform. Let’s compare the two models head-to-head.
Custodial Escrow: Trusting the Company
In custodial escrow, a company holds your crypto in their wallets. They control the private keys. When it’s time to release funds, a human (or their internal system) initiates the transfer.
This means you’re trusting that the company:
- Won’t get hacked (they’re a honeypot — one wallet holding everyone’s funds)
- Won’t freeze your funds due to regulatory pressure or internal policy
- Won’t disappear with your money (rug pull)
- Will actually release funds when they should
- Has proper internal controls (no rogue employee access)
History is littered with examples of custodial platforms failing: Mt. Gox, FTX, QuadrigaCX. The pattern is always the same — “trust us” followed by “sorry, the funds are gone.”
Non-Custodial Escrow: Trusting the Code
In non-custodial escrow, a smart contract on Ethereum holds the funds. No company, no individual, no server has access to the private keys — because there are no private keys to access. The funds are controlled entirely by the contract’s logic.
This means:
- No hack risk from the platform — there’s no central wallet to drain
- No rug pull possible — the platform can’t move funds that aren’t theirs
- No freeze risk — code doesn’t respond to legal threats or policy changes
- Platform can disappear and your funds are still safe in the contract
The tradeoff? You need to trust the smart contract code. But unlike trusting a company, you can actually verify the code. You can read it, audit it, or pay someone to audit it for you. Trust, but verify — and with smart contracts, verification is always possible.
Security Risk Comparison
| Security Risk | Custodial Escrow | Non-Custodial (Smart Contract) |
|---|---|---|
| Platform hack | 🔴 HIGH — central wallet is a target | 🟢 NONE — no central wallet exists |
| Rug pull | 🔴 POSSIBLE — company controls keys | 🟢 IMPOSSIBLE — code controls funds |
| Fund freeze | 🟡 POSSIBLE — regulatory or policy | 🟢 IMPOSSIBLE — code has no discretion |
| Smart contract bug | 🟢 N/A — no smart contract | 🟡 LOW — mitigated by audits |
| User error | 🟢 RECOVERABLE — support can help | 🔴 PERMANENT — no undo button |
| Insider threat | 🟡 POSSIBLE — rogue employees | 🟢 IMPOSSIBLE — no admin access |
The bottom line: custodial escrow is only as secure as the company behind it. Non-custodial escrow is as secure as the smart contract code — which, unlike a company, can be independently verified by anyone.
💡 Want to see non-custodial escrow in action? Zenland’s smart contracts are verified on Etherscan — you can read every line of code that governs your funds. Explore how Zenland works →
Dispute Resolution in Smart Contract Escrow
Security isn’t just about preventing theft — it’s also about having a fair process when buyer and seller disagree. This is where most escrow platforms are weakest, and where smart contract design really shines.
The Problem with Traditional Dispute Resolution
In traditional escrow (and most custodial crypto platforms), disputes are handled by customer support teams. The problems are obvious:
- Slow — weeks or months to resolve
- Opaque — you don’t know how decisions are made
- Biased — platforms may favor the party that generates more revenue
- Unaccountable — bad decisions have no consequences for the resolver
- Jurisdiction-limited — cross-border disputes are a nightmare
How Smart Contract Dispute Resolution Works
In a well-designed smart contract escrow, disputes follow a transparent, on-chain process:
- Buyer opens a dispute — this locks the escrow, preventing any releases
- Either party invites the pre-selected agent — the neutral third party chosen when the escrow was created
- Both parties submit evidence — screenshots, communication records, proof of delivery
- Agent reviews and decides — sets a percentage split (e.g., 70% to buyer, 30% to seller)
- Smart contract executes the split automatically — no manual transfers, no delays
The entire process is bounded by time limits. Agents typically have 7 days to respond. If they don’t, the process resets and parties can try again or negotiate directly.
The Staked Agent Model: Skin in the Game
Here’s where it gets interesting. In Zenland’s model, dispute agents aren’t just random people — they’re professionals who stake their own funds as collateral.
This creates a powerful accountability mechanism:
- Maximum Arbitratable Value (MAV) — an agent’s stake determines the maximum escrow value they can arbitrate. A $1,000 stake might allow arbitrating up to $5,000 escrows. This prevents an agent from making one corrupt decision on a massive deal.
- Slashing — if the DAO determines an agent acted unfairly, their stake can be partially or fully slashed (taken away). Bad behavior has real financial consequences.
- Reputation — agents build on-chain track records. Consistent fair resolutions lead to more business. Unfair decisions lead to slashing and loss of reputation.
Compare this to a customer support agent at a centralized platform who faces zero personal consequences for a bad decision. The incentive alignment is night and day.
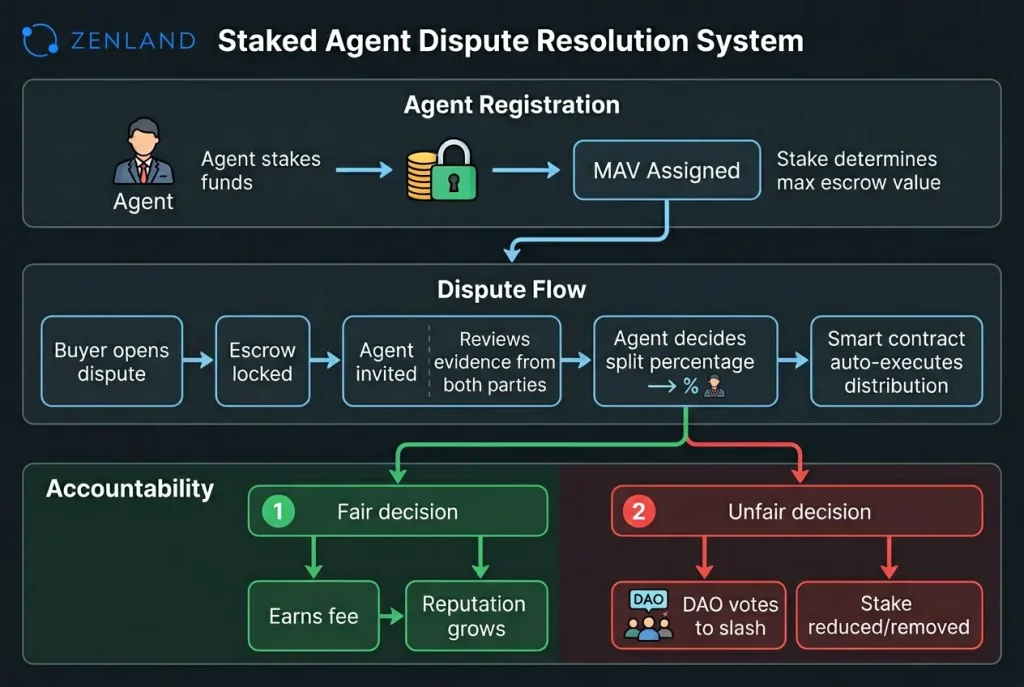
DAO Oversight: The Final Safety Net
Above the agents sits the DAO — a decentralized governance body of token holders who can:
- Vote to slash agent stakes for proven misconduct
- Adjust protocol parameters (fees, timeframes, MAV ratios)
- Add or remove supported tokens
- Upgrade the protocol through governance proposals
This creates a layered accountability system: agents are accountable to the DAO, and the DAO is accountable to its token holders. No single person or company makes unilateral decisions about the protocol.
Common Attack Vectors and How Escrow Contracts Defend Against Them
No discussion of smart contract security is complete without addressing the attacks that have plagued DeFi. Here’s how well-designed escrow contracts defend against the most common threats.
Reentrancy Attacks
The attack: A malicious contract calls back into the escrow during a withdrawal, draining funds before the balance updates. This is the attack that famously exploited The DAO in 2016.
The defense: Modern escrow contracts use the checks-effects-interactions pattern — updating internal state before transferring funds. Combined with OpenZeppelin’s ReentrancyGuard modifier, this attack vector is effectively eliminated.
Access Control Violations
The attack: Someone who isn’t the buyer calls the release() function, or someone who isn’t the seller calls refund().
The defense: Every state-changing function has strict role checks. Only the buyer can release. Only the seller can refund. Only the assigned agent can resolve disputes. These checks are enforced at the smart contract level — no amount of clever transaction crafting can bypass them.
Front-Running
The attack: A miner or MEV bot sees your transaction in the mempool and executes their own transaction first to gain an advantage.
The defense: Escrow contracts are largely immune to front-running because the operations are role-restricted. Even if someone sees your release() transaction, they can’t execute it themselves — only the buyer’s address can call that function. There’s no profit opportunity for front-runners.
Token Manipulation
The attack: Fee-on-transfer tokens or rebasing tokens cause the contract to receive less than expected, creating accounting mismatches.
The defense: Well-designed escrow platforms whitelist supported tokens and use SafeERC20 for all transfers. By only supporting known, audited tokens (like USDC and USDT), the risk of exotic token behavior is eliminated entirely.
Denial of Service
The attack: A malicious party tries to prevent the other from completing their action — for example, a contract that reverts when receiving funds, blocking a refund.
The defense: Using ERC-20 tokens (rather than native ETH) for escrow eliminates most DoS vectors, since token transfers don’t trigger fallback functions in the recipient. Additionally, time-based fallbacks ensure that no party can indefinitely block the process.
How to Verify a Smart Contract Escrow is Safe
You don’t need to be a Solidity developer to evaluate escrow security. Here’s a practical checklist anyone can follow.
1. Check Contract Verification on Etherscan
Go to the contract address on Etherscan and look for the green checkmark next to “Contract.” This means the source code has been published and matches the deployed bytecode. If the contract isn’t verified, that’s a red flag — you can’t see what the code actually does.
2. Look for Security Audits
Reputable escrow platforms publish audit reports from recognized security firms. Look for:
- The auditing firm’s reputation (Trail of Bits, OpenZeppelin, Consensys Diligence, etc.)
- The date of the audit (recent is better)
- Whether critical/high findings were addressed
- Whether the audited code matches the deployed code
3. Review Admin Privileges
Check if the contract has an “owner” or “admin” who can:
- Pause the contract
- Upgrade the logic
- Withdraw funds
- Change fee parameters
Some admin functions are necessary (like fee adjustments through governance), but the ability to withdraw user funds is an absolute dealbreaker. In a properly designed non-custodial escrow, no admin function should ever be able to touch escrowed funds.
4. Check On-Chain Activity
Look at the contract’s transaction history on Etherscan:
- How long has it been active?
- How many transactions has it processed?
- Are there successful completions (not just deposits)?
- Any suspicious patterns?
A contract with hundreds of successful escrow completions over months is far more trustworthy than one deployed last week.
5. Test with Small Amounts First
The simplest security measure: don’t start with your life savings. Run a small test escrow first. Go through the entire flow — create, fund, accept, fulfill, release. Verify everything works as expected before committing larger amounts.
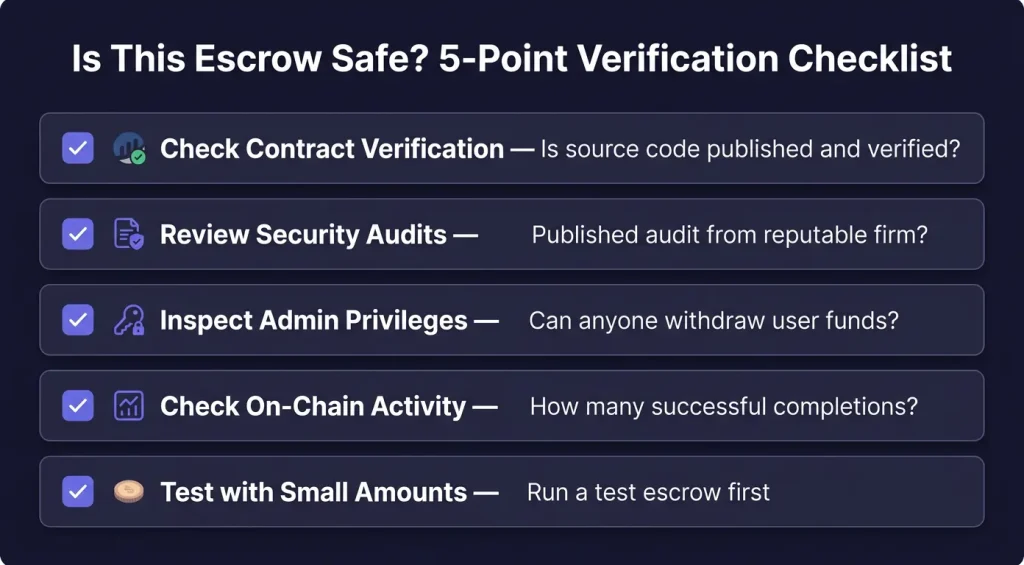
🔒 Verify it yourself. Zenland’s escrow contracts are verified on Etherscan with full source code visibility. No hidden functions, no admin backdoors. See the contracts in action →
Frequently Asked Questions
Can smart contracts be hacked?
Smart contracts can have bugs that attackers exploit, but “hacked” is often misleading. The blockchain itself isn’t compromised — rather, a flaw in the contract’s logic is exploited. This is why audits are critical. A well-audited escrow contract using established patterns (like OpenZeppelin libraries) has a very low risk of exploitable bugs. The key is choosing platforms that take security seriously: verified code, published audits, and battle-tested deployments.
What if the escrow platform disappears?
This is the beauty of non-custodial escrow. If the platform’s website goes offline, your funds are still in the smart contract on Ethereum. You can interact with the contract directly through Etherscan or any Web3 interface. The contract doesn’t need the platform to function — it’s autonomous code on the blockchain. This is fundamentally different from custodial platforms, where the company disappearing means your funds disappear too.
How are disputes really resolved?
In smart contract escrow with staked agents: the buyer opens a dispute, both parties submit evidence, and a pre-selected agent reviews the case. The agent decides a percentage split (e.g., 80% to buyer, 20% to seller), and the smart contract executes it automatically. Agents are incentivized to be fair because their staked funds can be slashed by the DAO if they act unfairly. The entire process typically resolves within 7 days.
Is Ethereum escrow safe for large transactions?
Ethereum is the most battle-tested smart contract platform, with the largest validator set and deepest security research community. For escrow specifically, Ethereum’s security is more than sufficient for large transactions. The main considerations are gas costs (which are fixed regardless of transaction size) and using stablecoins like USDC/USDT to avoid price volatility during the escrow period. Zenland’s $50 fee cap makes large transactions particularly cost-effective.
What’s the difference between smart contract escrow and multisig escrow?
Multisig escrow requires multiple parties to sign off on fund releases (e.g., 2-of-3 signatures). Smart contract escrow uses programmatic logic — state machines, time locks, and role-based access — to govern fund movement. Smart contract escrow is more flexible (supporting complex conditions, automatic timeouts, and percentage-based splits) while multisig is simpler but more limited. Many modern escrow platforms combine both approaches.
Do I need to understand Solidity to use smart contract escrow?
Not at all. Using smart contract escrow is as simple as using any Web3 app — connect your wallet, set your terms, and click buttons. The smart contract handles everything behind the scenes. Understanding Solidity helps if you want to verify the contract’s security yourself, but platforms like Zenland provide user-friendly interfaces that abstract away all the technical complexity.
Conclusion: Security Through Transparency
Smart contract escrow represents a fundamental shift in how we think about transaction security. Instead of asking “do I trust this company?”, you ask “can I verify this code?” — and the answer is always yes.
The security model is layered and robust:
- Open source code means anyone can verify the rules
- Non-custodial architecture means no company can touch your funds
- Payment protection mechanisms guard both buyer and seller at every stage
- Staked agents provide fair dispute resolution with real accountability
- DAO governance ensures the protocol evolves through community consensus, not corporate decisions
The next time someone asks you to “just trust them” with your crypto, remember: you don’t have to. Smart contract escrow lets you verify everything and trust nothing — which, in crypto, is exactly how it should be.
Verify Zenland’s Security Yourself →
Related Articles:
- What is Crypto Escrow? The Complete Guide for 2026 →
- Ethereum Escrow Services: Why Stablecoins Are the Future →
- How to Use Crypto Escrow: Step-by-Step Guide →
Last updated: March 2026



1 thought on “Smart Contract Escrow: How Blockchain Security Protects Your Funds”
Comments are closed.